Embedded Software: The Heart of the IIoT

Embedded software has played a role in opening the door for the next industrial revolution—the industrial internet of things. Specialized programming enables intelligent, connected machines to capture, aggregate and analyze data.
Latest News
April 1, 2018
Every now and then, a technology rises to prominence that plays a fundamental role in a transformative event. Embedded software is one such technology.
 Embedded software has played a role in opening the door for the next industrial revolution—the industrial internet of things. Specialized programming enables intelligent, connected machines to capture, aggregate and analyze data.
Embedded software has played a role in opening the door for the next industrial revolution—the industrial internet of things. Specialized programming enables intelligent, connected machines to capture, aggregate and analyze data.Long a part of the industrial automation infrastructure, this specialized programming, along with other key enablers, has opened the door for the next industrial revolution—the industrial internet of things (IIoT). Under this regime, manufacturers operate in a digital ecosystem, populated by intelligent, connected machines that capture, aggregate and analyze data as part of the production process. Armed with actionable information and unprecedented visibility, engineers and plant managers can optimize design, operational and maintenance processes in near real time.
“Embedded software is one of the key components in ‘smart products’—IoT connectivity is another,” says Nesrin Kecik, associate director and Industry X.0 smart products & embedded solution capability lead at Accenture Digital. “You simply can’t build IIoT solutions without embedded systems, and you cannot build embedded systems without embedded software. You also cannot leverage more recent methods like edge computing and edge analytics, which are already becoming more and more important in a number of scenarios.”
The fact is embedded software sets smart devices and systems apart from their predecessors. “Today, it’s the [embedded] software that decides about the quality of a device and the functionality it delivers to customers,” says Jeff Luszcz, vice president of product management at Flexera.
A close look at this specialized programming gives you a clearer understanding of where its power comes from. It also helps you understand why it is a springboard for the IIoT.
Setting the Stage
Basically, embedded software is a “system” that resides within a mechanical or electrical system, consisting of a sensor-based input system, an output actuator, a microcontroller and limited local memory. This type of programming performs predefined tasks—usually with very specific requirements—and varies in complexity, according to the functions it performs. Typically, users do not interact with embedded software. Instead, external controls activate its functions. Increasingly, devices containing the software communicate with other devices for calibration, diagnostics and data sharing.
Embedded software is sometimes erroneously referred to as firmware. Embedded software differs from firmware in that it is often the only code running on the hardware, while firmware passes control to an operating system, which then launches and controls programs.
Embedded code pervades factory production equipment and systems. These include smart sensors, industrial gateways, security systems and industrial controls like power line communications systems, picture archiving and communication system, computer numerical control systems, robotic systems, drives, actuators and motors.
“You simply can’t build IIoT solutions without embedded systems, and you cannot build embedded systems without embedded software.”
— Nesrin Kecik, Accenture Digital
Although manufacturers have found many uses for embedded software on the shop floor, deployment of the code has been constrained by the traditionally proprietary nature of automation equipment, devices and software. Proprietary systems can be expensive to purchase and maintain, and they usually are not designed for interoperability with other vendors’ products, limiting the buyer to one vendor and restricting choices of components. But perhaps more important is that adding features and upgrading systems is costly and difficult, often preventing the operator from taking advantage of the latest technological innovations.
Developers of embedded systems, however, hope that the trend toward open automation systems and the emergence of the IIoT will change this situation, opening new use cases in the process.
“Automation equipment usually falls into the ‘hard, real-time embedded systems’ category, a category that used to be dominated by proprietary software solutions,” says Omer Budak, associate manager and digital technology developer at Accenture Digital. “But now, open source software is making its way into the field, with more and more equipment using open source components, which have been validated or ‘battle tested’ for use with critical systems.”
The increasing momentum of the IIoT and the growing footprint of open source software promise to foster the proliferation of embedded software-empowered intelligent devices and smart sensors. This, in turn, will facilitate the creation of a robust digital environment at the network’s edge, opening the door for enhanced asset monitoring, data analytics, process alarming and process control on the shop floor, as well as the leveraging of artificial intelligence (AI) to enable machines to make sense of and act on complex data patterns.
For embedded software to take on more complex tasks, the systems encapsulating it have had to leverage a number of recent technological developments. Chief among these are advances in processor technology.
Flexibility and Complexity
Although processor developers continue to pursue performance levels dictated by Moore’s law, embedded system architects place a higher value on cost, power efficiency, integration and flexibility. This perspective stems from the unique demands placed on embedded systems, requiring more and more agility while relying on very limited resources. Reacting to these demands and the emergence of the IIoT, embedded processor vendors now increasingly tailor their products with a complex mix of computing technologies.
One way they’ve achieved this has been through the leveraging of multicore processors. Using this technology, chipmakers can construct a highly integrated system, dedicating individual processor cores to support multiple, separate operating environments, serving real-time and general-purpose operating systems with one computing unit. This reduces manufacturing and maintenance costs, eliminates redundant hardware and delivers greater processing agility.
These processors excel at applications involving repetitive tasks. For example, when reading a sensor in a manufacturing control application, the efficiency of a multicore processor enables a plant to tailor the frequency of sensor reads to increase its assembly line’s production speed. The same system could enable finer control of parts placement, opening the door for greater levels of miniaturization.
In addition to seeking greater agility, embedded system designers gravitate toward multicore processors because they allow the engineers to better harness AI. To meet this demand, companies like NVIDIA offer manycore processors that enable embedded designs to process AI-based software for image-recognition and real-time data acquisition and control applications.
Although multicore architectures offer considerable benefits to embedded system developers, these processors also place new demands on designers. To adapt their software, programmers must apply methods that ensure the efficient distribution of software functionality across the computing resources.
This means using a threading model, where the work can be broken down to separate execution units that run on different processors in parallel. If the threads are completely independent of one another, their design does not have to consider how they will interact. If the opposite is the case, the development process becomes more complicated. Overall, the incorporation of multicore processors requires more extensive testing and validation.
The Cost of Deterministic Behavior
Paralleling the rise of multicore processors, real-time operating systems (RTOSes) provide designers with the ability to take full advantage of the processors’ multitasking abilities. RTOSes differ from their predecessors in that they introduce a new level of abstraction, which enables more complex applications.
RTOSes also bring speed and deterministic behavior to embedded systems. These operating systems often have small footprints and support multithreading, which allows separation of software functionality into multiple, parallel tasks. This, in turn, gives the designer the ability to implement deterministic behavior by ensuring the availability of compute resources when required.
Using an RTOS can make it easier to design complex applications. The price for this simplification, however, is greater difficulty validating and debugging the code. In addition, designers often find that seemingly simple RTOS tasks result in surprisingly complex runtime behavior when executing as a system.
The fundamental challenge encountered in RTOS-based design stems from the fact that embedded applications have become increasingly complex, connected and event-driven, using peripherals that must be managed in parallel. RTOS tasks are not isolated. As a result, the designer must determine how the tasks are going to interact and share data using the RTOS services.
Code Writing Code
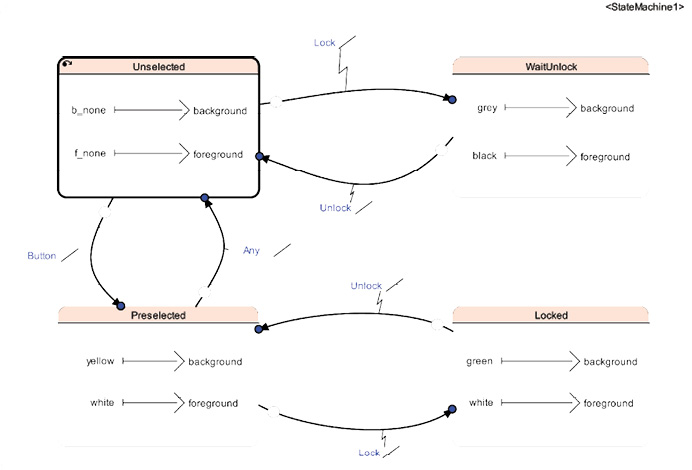 Automatic code generators aim to streamline the embedded software development process. ANSYS’ SCADE Suite KCG C code generator, shown here, reduces the time it takes to perform such tasks as code reviews and low-level testing. With this suite of tools, you can model the embedded software controls and then use the automatic code generator to produce C code that is a one-to-one replica of the model. Image courtesy of ANSYS.
Automatic code generators aim to streamline the embedded software development process. ANSYS’ SCADE Suite KCG C code generator, shown here, reduces the time it takes to perform such tasks as code reviews and low-level testing. With this suite of tools, you can model the embedded software controls and then use the automatic code generator to produce C code that is a one-to-one replica of the model. Image courtesy of ANSYS.To help embedded software developers deal with increasingly complicated projects within an acceptable timeframe, software development tool vendors offer automatic code generators, which significantly reduce the time required to complete embedded system design projects. Code generation tools allow developers to concentrate on specifying the problem, letting the generator deal with the implementation.
These tools are particularly adept at solving problems involving some kind of model or cases that cannot be elegantly solved by using a traditional library. Examples of these applications include providing code for parsers, finite-state machines, digital filters and I/O routing on modern microcontrollers.
Automatic code generators use model specifications as input. With this technique, the tool often computes a more efficient solution that contains less defects than a hand-coded solution. The model specification also doubles as documentation for the problem being solved.
Design for Security
The shift from isolated systems to connected “things” has increased cyber threats exponentially. Recognizing the scale of the safety and security risks confronting them, software developers have begun to rethink their methodologies.
Traditionally, safety and security have been seen as separated areas, but many industries now realize that embedded systems that are not cybersecure are not safe either. To address this, software developers need to have well-designed security gateways and architecture between safety “islands” and open systems.
“Cybersecurity requires a holistic approach—starting at the system level with threat and risk analysis—to understand cybersecurity requirements to be considered at the architectural design phase,” says Eric Bantegnie, vice president and general manager, systems business unit, at ANSYS. “This is why we have started to integrate cybersecurity risk analysis capabilities into our ANSYS medini tool suite, which covers systems safety analysis and system architecture design.”
This holistic approach means designers must go beyond the basics. “Clearly, we’ve understood that the ‘basics’—secure protocols, firewalls, data encryption, data source verification, authentication of both users and machines and so forth—aren’t enough,” says Kecik. “This is why design-for-security strategies have become part of software development, and rightfully so. ‘Distrustful’ subsystems, transparent interprocess comms, privilege separation and clearing resources upon free-up are becoming more important. Developers really can’t afford to ignore these principles and approaches.”
Software developers must also take steps to counter risks arising from the use of open-source resources. This means more governance around development processes to ensure suppliers apply as many layers of security as possible. For example, they need to make sure they ship a secure product and manage all vulnerabilities that come from open-source and third-party components.
“Tools for software composition analysis are specialized for this need and provide deep insight into what is being used, from open-source packages to copy and paste code that comes in during the development process,” says Luszcz. “Developers should scan for open-source components frequently as they build their projects. By managing open-source software and third-party components diligently throughout the whole software lifecycle, suppliers can maintain an accurate bill of materials and react quickly if vulnerabilities come up and need to be patched.”
The Edge and the Cloud
In addition to struggling to find ways of securing embedded systems, designers must also define embedded systems’ relationship with the cloud and the edge. Torn between demands for applications on the network’s edge and the power of the cloud, embedded software finds itself in the midst of an identity crisis.
Edge computing and edge analytics capabilities promise to play a critical role wherever robustness and low latency are required—just think about self-optimizing machinery. Here, the role of embedded software is certainly becoming more important.
“Cybersecurity requires a holistic approach—starting at the system level with threat and risk analysis—to understand cybersecurity requirements to be considered at the architectural design phase.”
— Eric Bantegnie, ANSYS
As these edge devices evolve, however, they begin to morph into something more than a traditional embedded system. “Most edge solutions become more powerful and lean towards high-end systems, which are somewhat different than classical embedded software principles,” says Kecik. “It is not uncommon that we see general-purpose operating systems, Java, Python and .NET technologies on these edge devices. Also, multicore and GPU hardware acceleration units are becoming popular on devices where edge analytics use cases are required. Embedded software is already ‘reacting’ to these changes. Secure connectivity, messaging protocols and device management, data collection or provisioning features are being utilized to support these capabilities, as are tools and frameworks.”
The bottom line? Embedded software has begun a transformation in which both the edge and the cloud play a part. What it will look like after its metamorphosis has yet to be decided.
“Embedded software was natively designed to be executed on the edge, but we now see new architectures, where several software functions—like diagnostics and monitoring for preventive maintenance of industrial assets—can also be executed on the cloud or within gateways in three-tier architectures,” says Bantegnie. “The industry is evolving into a richer paradigm, where modeling of IIoT systems has to encompass the various strategies of distribution—where actual embedded software functions are going to be executed.”
More Info
Subscribe to our FREE magazine, FREE email newsletters or both!
Latest News